20 Recommended Reasons For Deciding On A Zk-Snarks Wallet Website
Wiki Article
"The Zk-Powered Shield: How Zk Snarks Protect Your Ip And Identity From The World
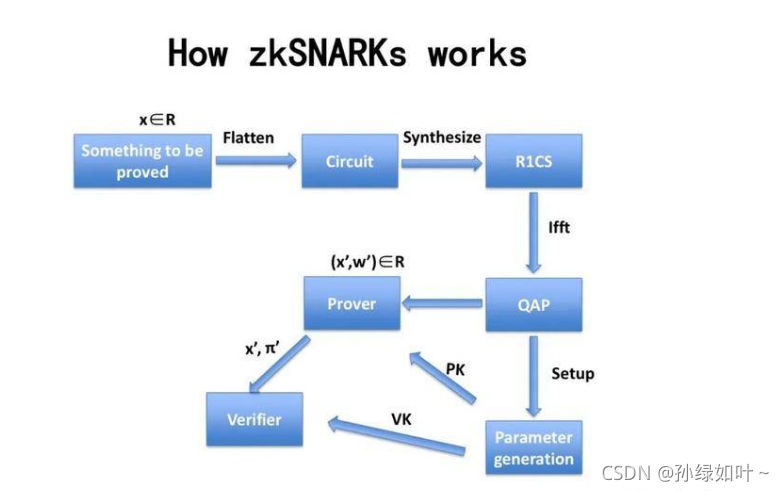
Since the beginning, privacy tools operate on the basis of "hiding in the crowd." VPNs funnel you through a server. Tor is able to bounce you around multiple nodes. It is a good idea, however they disguise the root of the problem by shifting it away, and not by convincing you that it isn't required to be disclosed. zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) introduce a distinct paradigm that can prove you are authorized for an action to be carried out without having to reveal who authorized it is that you're. It is possible to prove this in Z-Text. you can send a message through the BitcoinZ blockchain, and the Blockchain can determine that you're an authorized participant who has valid shielded addresses, however, it's still not able determine what account sent it. Your IP, or your identity and your presence in the conversation becomes mathematically unknowable to anyone else, yet legally valid for the protocol.
1. The Dissolution Of the Sender-Recipient Link
Even with encryption, reveal the relationship. One observer notices "Alice has been talking to Bob." Zk-SNARKs make this connection impossible. When Z-Text sends out a shielded message The zkproof verifies that the transaction is valid--that the sender is in good financial condition and the correct keys--without revealing an address for the sender nor the recipient's address. If viewed from a distance, it is seen as a security-related noise that comes out of the network itself, that is, not from a particular user. A connection between two distinct human beings is then computationally impossible verify.
2. IP address protection at the Protocol Niveau, not the Application Level.
VPNs as well as Tor help protect your IP because they route traffic through intermediaries. However these intermediaries also become new points of trust. Z-Text's implementation of zk_SNARKs is a guarantee that your IP's address will never be relevant to the process of verification. When you transmit your secured message on the BitcoinZ peer-to-peer network, it means you belong to a large number of nodes. The zkproof will ensure that when a person is monitoring the networks traffic, they are not able determine whether the incoming packet with the exact wallet that started it all, because the certificate doesn't hold that information. The IP's message becomes insignificant noise.
3. The Abolition of the "Viewing Key" Problem
In most blockchain privacy applications they have"viewing key "viewing key" that is able to decrypt transactions details. Zk-SNARKs as used in Zcash's Sapling protocol which is employed by Ztext, permit selective disclosure. You are able to demonstrate that you sent a message that does not divulge your IP address, any of your other transactions, or even the full content of that message. The proof in itself is not all that is you can share. This level of detail isn't possible in IP-based systems where revealing that message automatically exposes original address.
4. Mathematical Anonymity Sets That Scale Globally
Through a mixing program or a VPN, your anonymity is not available to all other users in that specific pool at that exact time. Through zkSARKs's zk-SNARKs service, your anonym has been set to every shielded email address in the BitcoinZ blockchain. Since the proof proves that the sender has *some* shielded address out of potentially millions of addresses, yet gives no specifics about the one it is, your protection is shared across the entire network. You're not a secretive member of a small room of peers or in a global community of cryptographic identifications.
5. Resistance to Attacks on Traffic Analysis and Timing Attacks
Highly sophisticated adversaries don't simply read IP addresses. They analyze their patterns of communication. They investigate who's sending data and when, as well as correlate the timing. Z-Text's use for zk-SNARKs combined with a blockchain mempool allows decoupling of events from broadcast. You may create a valid proof offline and release it later while a network node is able to broadcast the proof. The time of proof's presence in a block undoubtedly not correlated with day you built it, breaking the timing analysis process that frequently is a problem for simpler anonymity tools.
6. Quantum Resistance Through Secret Keys
It is not a quantum security feature. In the event that an adversary could log your traffic now before breaking the encryption you have signed, they will be able to connect the data to you. Zk's-SNARKs which is used in Z-Text, shield your keys from being exposed. Your public key is never divulged on the blockchain since the evidence proves that you've got the correct number of keys without the need to display it. The quantum computer, in the near future, will observe only the proof rather than the private key. Your private communications in the past are protected as the password used to verify them was never disclosed in the first place to be decrypted.
7. Unlinkable Identities Across Multiple Conversations
With only a single token and a single wallet seed, you can create multiple secured addresses. Zk-SNARKs permit you to show that you're the owner of these addresses, without divulging which. It is possible to engage in ten different conversations with ten distinct people. But no person, not even blockchain itself, can track those conversations through the exact wallet seed. The social graph of your network is mathematically fragmented by design.
8. Removal of Metadata as an attack surface
Security experts and regulators frequently say "we don't have the data we just need the metadata." These IP addresses constitute metadata. Your conversations with whom you are metadata. Zk's SARKs stand apart from privacy options because they block metadata within the cryptographic layers. The transaction itself contains no "from" or "to" fields, which are in plain text. The transaction does not contain metadata that can be used to provide a subpoena. Only the of the evidence. The proof will only show that an act took place, not who.
9. Trustless Broadcasting Through the P2P Network
When using an VPN you are able to trust the VPN service to not keep track of. When using Tor, you trust the exit node's ability to not be able to spy. Utilizing ZText, it broadcasts your zk proof transaction to BitcoinZ peer-to'-peer community. Then, you connect to some random nodes, transmit the details, then break off. Nodes are not learning anything, as the proof reveals nothing. It is impossible to know for sure that you're actually the creator, because you could be serving as a relayer for someone else. This network is a dependable host of sensitive information.
10. "The Philosophical Leap: Privacy Without Obfuscation
Finally, zk-SNARKs represent the philosophical shift beyond "hiding" and "proving with no disclosure." Obfuscation techs recognize that truth (your IP, your identity) is dangerous and must be kept hidden. Zk-SNARKs understand that the truth isn't important. Only the protocol needs to be aware that it is legally authorized. The shift from hiding in the reactive into proactive obscurity is what powers the ZK protection. Your identity and your IP do not remain hidden. They only serve to enhance the role of the network thus they're never needed as a result of transmission, disclosure, or even request. Read the most popular blockchain for website advice including text privately, messenger text message, encrypted messenger, encrypted message, instant messaging app, instant messaging app, text messenger, private message app, messenger text message, encrypted in messenger and more.
Quantum-Proofing Your Chats : Why Z-Addresses (And Zk-Proofs) Resist Future Decryption
The quantum computing threat has been discussed in abstract terms--a future boogeyman that could break encryption in all its forms. However, the truth is much more subtle and urgent. Shor's algorithm by a powerful quantum computing device, could break the elliptic-curve cryptography that protects the majority of internet and even blockchain. The reality is that not all encryption techniques are similarly vulnerable. Z-Text's underlying architecture, built on Zcash's Sapling protocol as well as zk-SNARKs provides inherent features that make it resistant to quantum encryption in ways traditional encryption can't. The main issue is what is revealed and what remains concealed. In ensuring that your private passwords remain private on the blockchain Z-Text protects you from an insufficient amount of information for a quantum computer to target. All of your conversations in the past, as well as your identification, and even your wallet remain sealed, not by complexity alone, but through invisible mathematics.
1. The Essential Vulnerability: Explicit Public Keys
To understand why Z-Text is quantum-resistant is to first realize why many systems not. When you make a transaction on a standard blockchain, your public keys are revealed when you spend funds. Quantum computers are able to access this public key, and utilize Shor's algorithm create your private key. Z-Text's protected transactions, which use z-addresses, never expose that public secret key. The zk-SNARK proves you have the key and does not divulge it. Public keys remain secret, giving quantum computer nothing to hack.
2. Zero-Knowledge Proofs of Information Minimalism
ZK-SNARKs are intrinsically quantum-resistant since they are based on the difficulty of issues that cannot be too easily resolved by algorithmic quantum techniques like factoring or discrete logarithms. But more importantly, the proof itself is completely devoid of detail about the key witness (your private password). Even if a quantum machine could possibly break the proof's underlying assumptions, it's not going to have anything to work with. This proof is an insecure cryptographic solution that makes a assertion without its substance.
3. Shielded Addresses (z-addresses) as being obfuscated existence
A z-address within Z-Text's Zcash protocol (used by Z-Text) is never recorded onto the Blockchain in a way that has a link to a transaction. If you are able to receive money or messages, the blockchain keeps track of the shielded pool transaction has occurred. Your particular address is within the merkle tree notes. A quantum computer scanning this blockchain is only able to view trees and proofs, not leaves or keys. It is encrypted, however it is not visible to the eye, which makes its existence invisible to retrospective examination.
4. Defense: The "Harvest Now, Decrypt Later" Defense
Quantum threats are the biggest threat to our society today. It has nothing to do with active threats that is passively collected. Cybercriminals can grab encrypted information on the internet and then store it, waiting for quantum computers to develop. In the case of Z-Text the adversary could search the blockchain for information and obtain the transactions that are shielded. However, without access to the viewing keys and never having access to public keys, they have little to decrypt. They collect made up of proofs with no knowledge made by design to will not have encrypted messages which they could later decrypt. The message is not encrypted in the proof. The evidence is merely the message.
5. The significance of using a single-time key of Keys
Many cryptographic systems allow reuse of keys creates open data available for analysis. Z-Text, built on the BitcoinZ Blockchain's version of Sapling allows the implementation of diversified addresses. Each transaction may use an unlinked, new address generated from the exact seed. That is, should one transaction be breached (by other means that are not quantum) and the others are secure. Quantum immunity is enhanced due to the continuous key rotation which restricts the usefulness of a single key that is cracked.
6. Post-Quantum Asumptions in ZK-SNARKs
Modern zk SNARKs usually rely on pairs of elliptic curves that are theoretically vulnerable to quantum computer. However, the design that is used in Zcash and ZText is able to be migrated. The protocol was created for eventual support of post-quantum secure Zk-SNARKs. Since the keys can never be divulged, the change to a new proving system can happen through the protocol, not needing the users to release their history. The shielded pool design is advance-compatible with quantum resistance cryptography.
7. Wallet Seeds and the BIP-39 Standard
Your wallet seed (the 24 words) doesn't have to be quantum-secure as. The seed is actually a massive random number. Quantum computers aren't much faster at brute-forcing the 256 bits of random number than the classical computer because of the Grover algorithm's weaknesses. There is a vulnerability in the determination of public-keys from this seed. In keeping the public keys in a secure way using zk SNARKs, the seed stays secure, even during a postquantum age.
8. Quantum-Decrypted Metadata vs. Shielded Metadata
If quantum computers ultimately breach encryption in some ways yet, they face issues with Z-Text's inability to conceal metadata from the protocol layer. If a quantum machine is able to prove that an transaction occurred between two parties if they had their public keys. In the event that those keys weren't disclosed, as well as the transaction is non-zero-knowledge proof and doesn't contain information about the address, then the quantum computer is able to only determine that "something occurred in the shielded pool." The social graph and the timing or frequency of events remain unseen.
9. Merkle Tree as a Time Capsule. Merkle Tree as a Time Capsule
Z-Text stores the messages stored in the blockchain's merkle tree of Shielded Notes. This architecture is intrinsically resistant quantization because, the only way to discover a particular note there must be a clear understanding of the dedication to a note as well as the location in the tree. Without a key for viewing, it is impossible for quantum computers to discern your note from millions more in the tree. The time and effort needed to searching the entire tree for the specific note is staggeringly large, even for quantum computers. It increases by each block that is added.
10. Future-proofing By Cryptographic Agility
In the end, the primary part of ZText's quantum resistance is its cryptographic aplomb. The system is built on a blockchain protocol (BitcoinZ) which is improved through consensus among the community, cryptographic protocols can be exchanged as quantum threats emerge. There is no need to be locked into a single algorithm forever. Their history is covered and their key is kept in a self-pursuant manner, they're able to switch onto new quantum-resistant models and not reveal their old ones. The architecture ensures that your messages are secured not just against the threats of today yet also for the ones to come.